Security leadership crisis
Only 35,000 CISOs worldwide serve around 359 million businesses. A new report warns of a massive structural imbalance that leaves small and mid-sized companies dangerously unprotected.
Risk rising fast
The rapid proliferation of artificial intelligence is delivering not just efficiency gains but also a fast-growing set of security challenges. A recent analysis by TrendAI reveals that vulnerabilities in the AI ecosystem are expanding significantly faster than in the broader software landscape, and many organizations are struggling to keep
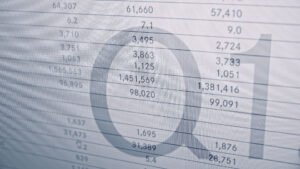
Criminals study cycles
Organisations assume cyber threats remain constant throughout the year, spreading risk evenly across all four quarters. This misconception leaves them vulnerable during a period when attackers are most active.
Blackout by AI
In an unusually specific forecast, renowned research and advisory firm Gartner is warning of an impending catastrophic scenario.
A free AI agent with no guardrails
The developments surrounding OpenClaw are generating equal parts fascination and serious security concern. The makings of a genuine enterprise nightmare are already visible.
Transparency alone is not enough
Operational resilience in OT environments requires concrete technical and organizational levers: access controls, robust test environments, and compensating measures for legacy systems. At the same time, the supply chain is moving to the center of attention as both an attack vector and a compliance factor.
OPSWAT Threat Landscape Report 2025
A new report demonstrates that conventional security systems are failing to identify many contemporary threats. OPSWAT highlights critical blind spots in current defenses and advocates for a fundamental overhaul of cybersecurity strategies.
Rethinking security strategy
The days when cyber security was an afterthought are over. The EU Cyber Resilience Act (CRA) and the EU’s new Product Liability Directive make it clear: software must be secure from the outset. “Security by design” is thus turning from a buzzword into a survival strategy. Cycode shows how
Nationwide cyber attack in the USA
The series Zero Day deals with the current cyber threat landscape and addresses the consequences of a large-scale cyberattack in the USA. For exactly one minute, electricity, mobile networks, server systems, traffic control systems, and air traffic control systems fail simultaneously across the entire country. The attack costs over
Most Read Articles

7. May 2026

4. May 2026