Organisations assume cyber threats remain constant throughout the year, spreading risk evenly across all four quarters. This misconception leaves them vulnerable during a period when attackers are most active.
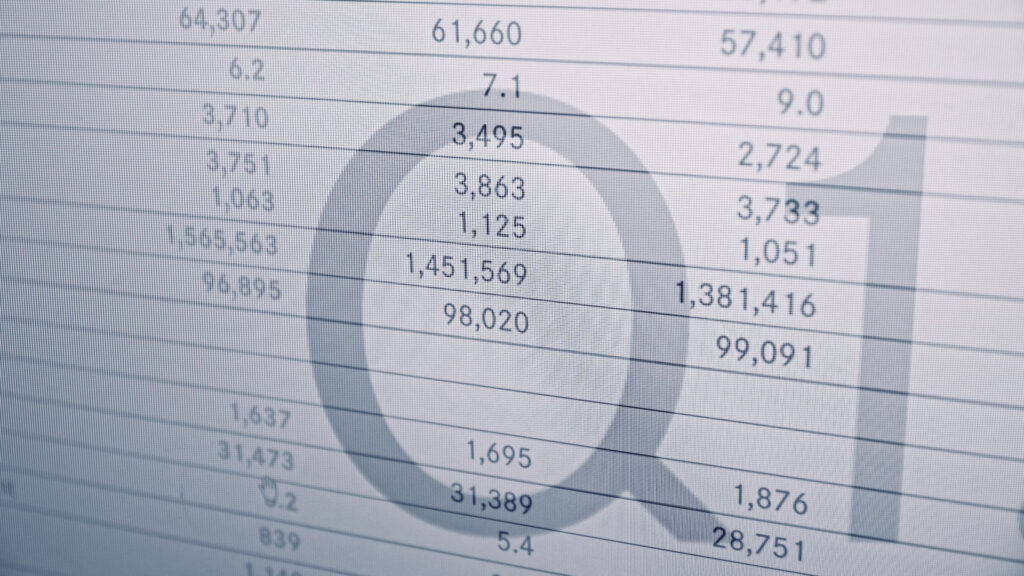
Over 2,200 victims of ransomware were listed on leak sites in Q1 2025, marking a 35% jump from the previous quarter.
The first quarter represents a perfect storm of security weaknesses: systems remain unpatched from holiday backlogs, new infrastructure gets deployed without proper hardening, and security teams face budget constraints while adjusting to new priorities.
Danny Mitchell, Cybersecurity Writer at Heimdal, a cybersecurity company delivering unified, AI-powered protection platforms, explains why the early months create such dangerous conditions.
“Attackers understand business cycles better than most security teams realise,” Mitchell says. “They know Q1 is when patch deployment slows, when security budgets reset, and when IT teams are still catching up from year-end backlogs.”
Below, Mitchell reveals why Q1 consistently emerges as the riskiest period for cyber threats and what organisations should prioritise to close this early-year security gap.
Why cybercriminals love Q1
Attackers don’t choose their timing randomly. They study organisational behaviour patterns and strike when defences are weakest. Q1 represents a convergence of vulnerabilities that creates ideal conditions for successful breaches.
Patch delays and work backlogs
The holiday period leaves a backlog of unpatched systems. Security teams reduce staffing during December, postponing critical updates until the new year.
When January arrives, these teams face competing priorities: onboarding new employees, implementing fresh policies, and managing budget adjustments. Patch deployment gets delayed further, sometimes by weeks.
“The gap between vulnerability disclosure and patch deployment widens significantly in Q1,” Mitchell explains. “Organisations that typically patch within 48 hours might take two weeks or more during this period. Attackers know this and maintain databases of recently disclosed vulnerabilities specifically to exploit during this window.”
Predictable business cycles
Business cycles become predictable attack vectors:
- Companies reset their budgets, which means security spending often gets frozen whilst procurement processes restart.
- New projects launch, bringing hastily configured infrastructure that hasn’t undergone proper security review.
- Remote workers return from holidays with personal devices that may have been compromised, creating fresh entry points into corporate networks.
Operational complacency compounds these issues. Security teams assume the post-holiday period will be quiet, matching the reduced activity they experienced in December. This assumption proves dangerous. Whilst organisations slow down, attackers accelerate their campaigns.
“We consistently observe attackers ramping up reconnaissance activities in late December, preparing to strike in January when their research shows the highest probability of success,” Mitchell notes.
The threats that spike at the start of the year
Mitchell says there are three specific attack types that show marked increases during Q1, each exploiting the unique vulnerabilities this period creates.
1. Ransomware
Ransomware campaigns surge as attackers target organisations with delayed backups and unpatched systems. The 35% quarterly increase in ransomware victims demonstrates how effectively criminals exploit this timing.
They understand that companies facing year-end financial pressures may be more likely to pay ransoms quickly, particularly if recovery processes haven’t been tested recently.
2. Credential Theft
Credential theft intensifies as attackers harvest login details from holiday-compromised devices and exploit password reuse across personal and professional accounts. Employees frequently change passwords at year-end for administrative reasons, but they often choose weak variations or reuse patterns that automated tools easily crack.
“Credential stuffing attacks increase by roughly 40% in Q1 because attackers know organisations have larger numbers of recently changed but poorly chosen passwords,” Mitchell explains. “They’re also targeting new employee accounts that may not have proper multifactor authentication configured yet.”
3. Supply Chain Exploits
Supply chain exploits gain traction during this period.
Vendors rush to deploy new versions of software at the start of the year, sometimes bypassing rigorous security testing to meet project deadlines. Attackers monitor these release cycles, identifying vulnerabilities in widely deployed business applications before organisations can patch them.
These threats thrive because they exploit systemic weaknesses rather than individual mistakes, making them particularly difficult to defend against without proactive security measures.
How businesses can close the patch gap
Organisations can significantly reduce Q1 vulnerability by implementing specific measures before the period begins.
Patch Automation
Patch automation represents the most effective defence. Manual patching processes break down when security teams face reduced capacity and competing priorities.
Automated systems maintain consistent deployment schedules regardless of staffing levels or workload pressures. These solutions can identify missing patches, test them in controlled environments, and deploy them systematically without human intervention.
Asset Visibility
Security teams cannot patch systems they don’t know exist. Many breaches occur because shadow IT or forgotten legacy systems remain unpatched for months.
Comprehensive asset management platforms provide real-time inventory of all devices, applications, and infrastructure components, ensuring nothing escapes the patching process.
“You cannot secure what you cannot see,” Mitchell states. “Organisations that implement continuous asset discovery reduce their attack surface dramatically because they eliminate the blind spots attackers typically exploit.”
Security Hygiene
Security hygiene practices require reinforcement before Q1 begins. This includes verifying backup systems function correctly, confirming multifactor authentication is enabled across all accounts, and reviewing access controls to ensure departing employees no longer have system access.
These foundational measures prevent common attack vectors from succeeding.
Regular security assessments should occur in November and December, identifying vulnerabilities before the holiday period rather than discovering them in January when response capacity is limited. This proactive approach shifts the security posture from reactive to preventative.
Danny Mitchell, Cybersecurity Writer at Heimdal, further commented:
“Organisations entering Q1 should prioritise five immediate actions to close the patch gap. First, enable automated patch management across all endpoints and servers before year-end. Second, conduct a complete asset inventory to identify systems that might have been missed during holiday periods. Third, verify that backup systems are functioning and test recovery procedures. Fourth, enforce multifactor authentication on all accounts, particularly for new employees starting in January. Fifth, schedule vulnerability assessments for late December rather than waiting until the new quarter begins.
The organisations that suffer breaches in Q1 are the ones that delayed these fundamental steps. Attackers count on this delay. By implementing these measures before the holiday period, you eliminate the window of vulnerability they’re planning to exploit.”
(lb/Heimdal)