The era of simple passwords is coming to an end. But while companies worldwide are adopting multi-factor authentication (MFA), a dangerous fallacy is emerging: a one-time query of a second factor does not make a system truly secure in the sense of Zero Trust.
We analyze why the majority of passwordless projects fail, what security gaps even modern MFA still has, and why analysts like Gartner and Forrester believe that passkeys combined with continuous authentication are the only viable path forward.
Digital identity is the new perimeter. This insight is not new in IT security, but implementation often lags behind requirements. While some are still debating the introduction of multi-factor authentication, experts from Gartner and Forrester are already discussing how to overcome the password concept through passkeys and integrate continuous verification into corporate networks. An analysis of current market data and analyst reports reveals a split picture: between the technological utopia of a completely passwordless world and the grim reality of outdated legacy systems, industrial control systems, and human habits.
The Brutal Reality: Why Passwords and Even MFA Are Not Silver Bullets
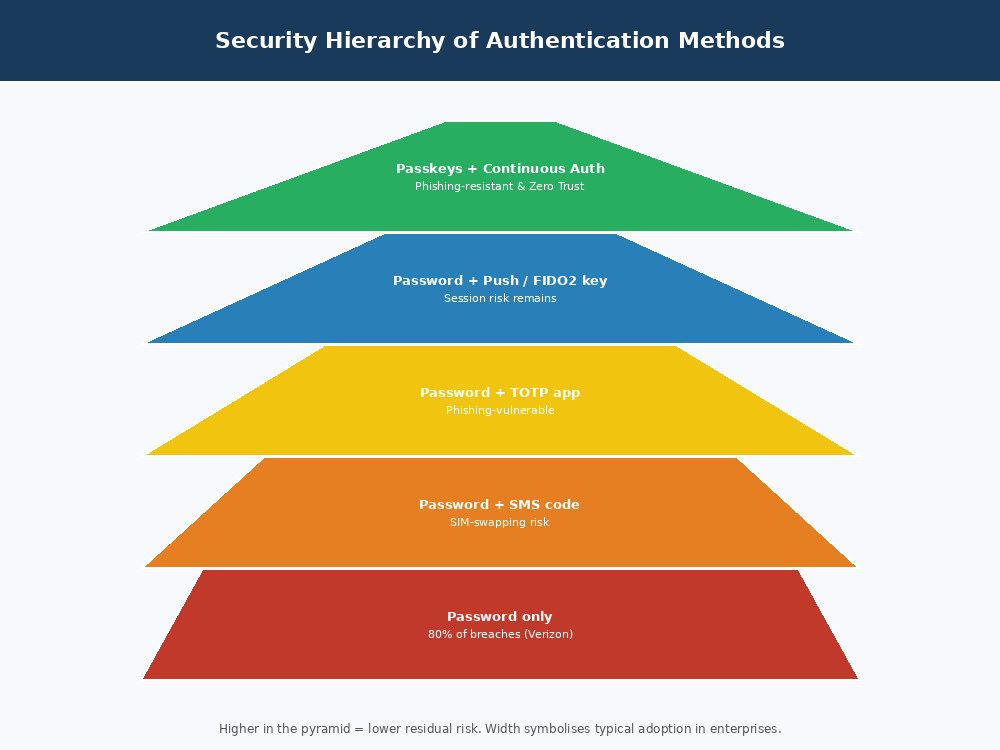
The numbers are alarming but clear. Stolen credentials remain the preferred route for cybercriminals. The Verizon Data Breach Investigations Report 2024 shows that 68 percent of all security breaches are attributed to human error. Attackers simply log in. They no longer hack their way through complex firewalls. According to Microsoft’s Digital Defense Report 2023, over 90 percent of compromised corporate accounts are those that had not implemented MFA.
Even where MFA has been implemented, new attack vectors emerge. Traditional MFA using SMS codes is vulnerable to SIM swapping. TOTP apps can be bypassed by specially crafted phishing pages that intercept both the password and the six-digit code in real time. Particularly insidious is so-called MFA fatigue or push bombing, where attackers send so many push notifications that victims finally consent out of frustration. Gartner predicts in its Hype Cycle for Digital Identity that by 2026, 70 percent of all identity-related incidents will still be attributable to remaining password stores.
“According to Forrester analyst Andras Cser, the biggest problem is not the technology but the lack of a roadmap for legacy integration.”
The Apparent Contradiction: MFA and Zero Trust
One of the most provocative theses in current security debates is that MFA and Zero Trust fundamentally contradict each other. The Zero Trust model, as defined by NIST SP 800-207, is based on the principle of “Never Trust, Always Verify.” Every request, every access, every action must be continuously checked. Traditional MFA, however, implements the opposite: a user authenticates strongly once and then receives a session cookie that is often valid for hours or even days. This is a clear contradiction to continuous verification.
Forrester emphasizes in its report “Top Trends Shaping Identity And Access Management 2025” that companies need to move away from point-in-time checks. The future belongs to continuous authentication, where user behavior is constantly monitored and evaluated, including mouse movements, typing speed, location, device, network, and a dynamic risk score. MFA is not the problem – the one-time, long-lived trust zone after authentication is.
Passkeys: The Savior or Just Hype?
Passkeys are based on the FIDO2 and WebAuthn standard and are inherently phishing-resistant. A passkey is bound to the specific origin of the website or app, meaning a fake login attempt would fail because the browser recognizes the wrong address. A passkey is by definition two-factor, combining possession of a device with the user’s biometrics – making the traditional password and often the separate MFA app obsolete.
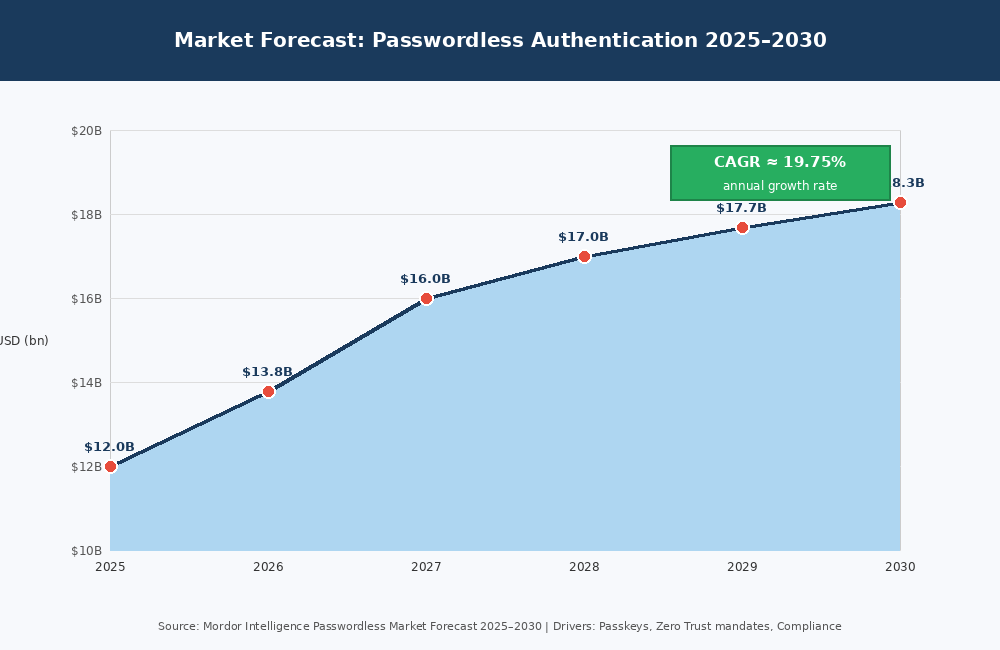
Gartner positions passkeys in the Hype Cycle for Digital Identity as a technology just reaching the “Slope of Enlightenment”, meaning it is becoming suitable for mass adoption. Mordor Intelligence forecasts an average annual growth rate of nearly 20 percent and a market volume of over $18 billion USD by 2030, driven primarily by Apple, Google, and Microsoft.
However, an RSA report from 2025 shows that 90 percent of companies report significant problems when introducing passwordless solutions. Not due to the technology itself, but due to heterogeneous IT landscapes. Realistically, coverage of 75 to 85 percent of all systems is achievable with today’s technologies.
The Dangerous Fallback Trap
One of the greatest dangers when introducing passwordless systems is the fallback mechanism. Many vendors implement an automatic fallback to the classic password for convenience if biometric authentication fails. This is precisely counterproductive: attackers can specifically try to force the system into a state where it reverts to the weaker password. The only secure solution is to implement redundant passwordless recovery mechanisms: backup authenticators, physical security keys, or cloud backups of passkeys. Under no circumstances should a password be allowed as a fallback.
Looking into the Crystal Ball: IAM 2026 and the Cost of Non-Implementation
The HID Global Blog succinctly summarizes expectations for 2026: “Passwordless becomes the corporate baseline.” Gartner and Forrester agree that up to 50 percent of all IT helpdesk tickets concern classic password resets. A single reset costs a company an average of about $70 USD when factoring in helpdesk labor, employee productivity loss, and frustration costs. For a mid-sized company with a thousand employees, this “password tax” quickly adds up to over $140,000 USD annually – without a single security incident.
Real-world example: A European financial services provider reportedly reduced helpdesk costs by approximately 40 percent after introducing passwordless authentication, according to a publicly available analyst report. This underscores the economic lever beyond pure security considerations.
| Method | Security Level | Phishing Resistance | Zero Trust Ready | Usability | Costs |
| Password only | Very low | No | No | High | Low |
| Password + SMS code | Low | No | No | Medium | Low |
| Password + TOTP app | Medium | Partially | No | Medium | Low |
| Password + Push notification | Medium-High | Partially | Partially | High | Medium |
| Password + FIDO2 key | High | Yes | Partially | Low | High |
| Password (FIDO2) | Very High | Yes | Yes (basis) | Very High | Medium |
| Password + Continous Auth | Extreme | Yes | Yes (full) | High | High |
Comparison of Authentication Methods in the Zero Trust Context
(Source: Compiled from Microsoft Learn, NIST SP 800-63B, and analyst reports from Gartner and Forrester.)
| Implementation Pitfall | Typical Symptom | Recommended Solution |
| Legacy apps without FIDO2 | Old ERP/HR systems block adoption | Deploy Identity-Aware Proxy (IAP) or Reverse Proxy |
| Missing backup strategy | Locked out when device fails | Redundant passkeys on separate devices / hardware tokens |
| MFA fatigue / push bombing | Employees consent out of frustration | Switch to number matching or FIDO2; abolish pure push MFA |
| Insufficient session shortening | Long-lived sessions violate Zero Trust | Short-lived tokens (minutes not hours) with refresh mechanisms |
| Lack of end-user acceptance | MFA bypassed or ignored | Gradual migration with pilot groups; clear security communication |
Common Implementation Pitfalls in Passwordless and MFA Projects
(Source: RSA Passwordless Deployment Report 2025, Okta Secure Sign-in Trends 2024, Forrester IAM Best Practices.)
Practical Recommendations: What Companies Should Do Now
Step 1: Eliminate insecure MFA methods
Companies should remove SMS codes and pure push notifications without number matching from their portfolios. According to NIST SP 800-63B, these methods are no longer considered state-of-the-art. Instead, focus on FIDO2 – via platform authenticators like Windows Hello, Face ID, or Touch ID, or via physical security keys.
Step 2: Modernize session management
Token lifetimes must be drastically shortened. The Zero Trust model requires verification within minutes or even seconds. Modern identity providers allow step-up authentication for security-relevant actions without requiring users to completely restart each time.
Step 3: Secure legacy systems
Identity-Aware Proxies place a modern authentication layer in front of old applications without requiring changes to legacy application source code. This is the most pragmatic approach for companies with long-lived industrial plants or heavily regulated environments.
Step 4: Introduce passkeys and build a roadmap
The major operating systems support passkeys natively, and many identity providers have already implemented corresponding interfaces. Companies should now begin testing passkeys in pilot projects and create a roadmap for the gradual replacement of passwords – with redundant backup mechanisms that avoid password fallbacks.
Conclusion: MFA Is Not Dead – But the Way It Is Implemented Must Change
MFA has not failed, but the traditional, point-in-time implementation is no longer sufficient for a Zero Trust world. The future belongs to combined, continuous authentication based on passkeys and behavioral analytics. Phishing resistance and user-friendliness are no longer mutually exclusive thanks to FIDO2 and passkeys. The biggest hurdle today is no longer the technology, but the willingness of organizations to overcome old habits and outdated systems. Companies that tackle this change now gain a competitive security advantage and save significant operational costs long-term.
Q&A: The Most Important Questions About Modern Authentication
Has MFA really failed because no one uses it correctly?
No. The technology itself is solid, but implementation is often lacking. According to Okta Secure Sign-in Trends, only about 30 to 40 percent of enterprise customers use MFA at all, and even then, insecure methods like SMS are often preferred. MFA fails where it is treated as a mere compliance checkbox without following Zero Trust principles.
Are passkeys the solution to all MFA problems?
Yes, with regard to phishing. Passkeys significantly eliminate the risk of stolen credentials. However, they do not solve the problem of session hijacking after successful login – this still requires continuous risk assessment and short-lived tokens.
What is the concrete cost of not implementing modern authentication?
Beyond compliance risks from GDPR and future regulations like eIDAS 2.0, there are the direct costs of data breaches. Added to this are operational costs for password resets, which according to Gartner account for about 50 percent of all helpdesk tickets. An average password reset costs around $70 USD.
Are biometric methods secure enough?
Gartner warns: By 2026, about 30 percent of companies will no longer consider biometric methods trustworthy solely due to AI-generated deepfakes. Biometrics should always be used as one factor within a passkey system, never as the sole secret.
Can Zero Trust work without continuous MFA?
No. Zero Trust without strong identity verification is impossible. Traditional, one-time MFA is not enough. Zero Trust requires permanent verification across the entire session: short-lived tokens, context-aware access decisions, and behavioral analytics.